Julianne Margaret V. Ugali
THIRD QUARTER ACTIVITIES
ACTIVITY 1: Different ways people can use a Computer.
In school:
- Gamified learning
- Digital field trips
- Integrate social media
- Gather student feedback
- Creating digital content
- Using a shared, online classroom calendar
- Review and critique webpages
- Incorporate video and multimedia into lessons and presentations
- Online activities for students who finish work
At work:
- Writing, reading and answering emails Computers are used in many ways in an office.
- They’re used to make calculations that would take too much time to do by hand. This includes financial, economic, technical, mathematical and much more than those.
- Computers are also used to keep track of money flows, administration, making drawings for mechanics, building websites like Quora and maintenance/monitoring of buildings.
At home:
- Online bill payment
- Watching movies or shows at home
- Home tutoring
- Social media access
- Playing games
- Internet access
ACTIVITY 2: 5 Internet Threats
1. Malware
Malware is malicious software such as spyware, ransomware, viruses and worms. Malware is activated when a user clicks on a malicious link or attachment, which leads to installing dangerous software. Cisco reports that malware, once activated, can:
2. Phishing
Phishing attacks use fake communication, such as an email, to trick the receiver into opening it and carrying out the instructions inside, such as providing a credit card number. “The goal is to steal sensitive data like credit card and login information or to install malware on the victim’s machine,” Cisco reports.
3. Spam:
Spam refers to unsolicited messages in your email inbox. From the sender’s perspective, spam is a great way to get their message across in an efficient and cost-effective way. While spam is usually considered harmless, some can include links that will install malicious software on your computer if the recipient clicks on it.
4. Phishing
Created by cybercriminals attempting to solicit private or sensitive information, phishing schemes tend to be the starting point of nearly all successful cyberattacks. Phishing schemes can disguise itself in many forms, whether its posing as your bank or a common web service, with the sole purpose to lure you in by clicking links and asking you to verify account details, personal information, or passwords. Many people still associate phishing threats with emails, but the threat has evolved beyond your inbox. Hackers are now employing text messages, phone calls, phony apps, and social media quizzes to trick an unwitting victim.
5. Computer Worm:
The distinctive trait of a worm is that it can self-replicate and doesn’t require human interaction to create copies and spread quickly and in great volume. Most worms are spread though tricking internet users and are designed to exploit known security holes in software. Since many employees use their phones for work-related tasks when they are not within the perimeter of their corporate firewall, businesses are at a high risk for potential worms. If a machine is infected, the worm can: corrupt files, steal sensitive data, install a backdoor giving cybercriminals access to your computer, or modify system settings to make your machine more vulnerable.
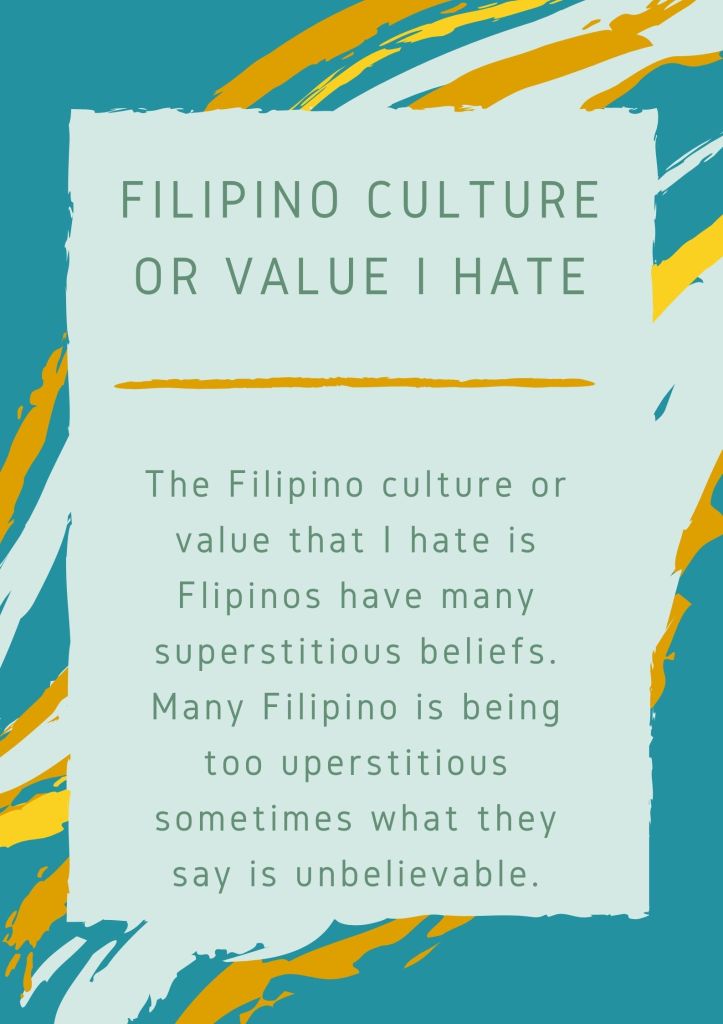
ACTIVITY 3: What is the value/culture of a Filipino that you like and hate the most?
ASSIGNMENTS
ASSIGNMENT 1: What is Computer
A computer is a machine that can be instructed to carry out sequences of arithmetic or logical operations automatically via computer programming. Modern computers have the ability to follow generalized sets of operations, called programs. These programs enable computers to perform an extremely wide range of tasks.
ASSIGNMENT 2: What is the connection of Internet and World Wide Web?
In simple terms, the World Wide Web is just one common area for information exchange, facilitated by global computer networks or the Internet. You connect to this Internet to access the Web, but the Internet is just the connection between countless, separate servers, computers, and devices.
ASSIGNMENT 3: Rules of Netiquette
How many hours do you spend on the Internet per day?
• I spend 10 hours a day because we have online class. it’s really difficult for me because we need to attend online class.
Can you leave without Internet for a week?
• Yes, I’d love to. Because when the time where internet is still not being invented or created life was so simple and full of joy. Almost everyone were healthy because they are far from the reach of people’s judgements or negative thoughts and opinions. They sleep on the right time and eat on the right time. Everyone were doing things manually and little harder than what we have now but that makes everyone together and build good relationship to each other.
What positive or negative impact does Internet have on your life?
• The positive effect of gadgets in education, the internet is a great source of research.
• The negative effect of gadgets in education, as much as it is easy to research it is also easy to cheat especially in online classes.
How many times have you complained about your Internet connection speed?
• I complained almost of the time, it affects me with my learning. Most students including me use the internet to go to our online classes. Here we do our tests, activities, and we discuss. With bad internet connection we can’t properly learn.
ASSIGNMENT 4: Think Before You Click
For me, social media plays a major role in our society nowadays. Almost everyone has access and social media accounts. One image can spread faster than you can imagine and it can influence someone’s life enormously. Before you hit the like button and share something, ensure that you wouldn’t hurt somebody’s feeling. Be sensitive enough to the theme and idea of the image. For example, you see a picture of a woman wearing a short-revealing dress. The photo was taken when the woman is unaware of the situation. You as a responsible social media user, will never support this idea and you wouldn’t share this for others to see.
PERFORMANCE TASKS