Anjhelica Mae T. Villanueva
THIRD QUARTER
ACTIVITIES
Activity No.1
DIFFERENT WAYS PEOPLE USE COMPUTERS
In school
- They use it for presentations, teaching machines, online portal, and data saver.
At work
- They use a computer to connect to the Internet or use e-mail. They also use computer for spreadsheets, databases, and scheduling.
At home
- Computers can be used to play games, watch movies, pay bills, do homeworks, social media access, internet access, business, and education.
Activity No.2
5 Internet Threats
Spam
- is a term that is used to describe the fact that most email accounts have a ‘Spam’ or ‘Junk’ folder implies that spam emails are a major problem, with more than half of all emails destined for these folders. Spam emails are not a direct threat, apart from being annoying. Many, however, can contain malware.
Adware
- Adware is a form of malware that shows unwanted advertisements while a user is browsing the internet. Advertisements often redirect your searches to advertisement websites and gather marketing-type data about you without your knowledge, which is considered malicious.
Trojan
- Trojans leave your computer completely unprotected, allowing hackers to steal any information from it. Trojans sometimes disguise themselves as innocuous computer programs in order for hackers to gain access to your computer without being detected.
Phishing
- Phishing is a form of fraud. In its most basic form, phishing is a type of deception. Official-looking emails impersonating a well-known provider, such as a bank, are often sent. These emails are being sent in order to obtain people’s passwords and credit card information.
Spyware
- Spyware is another form of malware. Spyware is an all-encompassing internet nastiness that is often associated with downloadable file pop-ups. Spyware will record your keystrokes, read and remove your files, reformat your hard drive, and access your applications once it is installed on your device. Without your knowledge, whoever controls the spyware has access to your personal information.
Activity No.3
Filipino Culture that you hate & love
Activity No.4
16 personalities
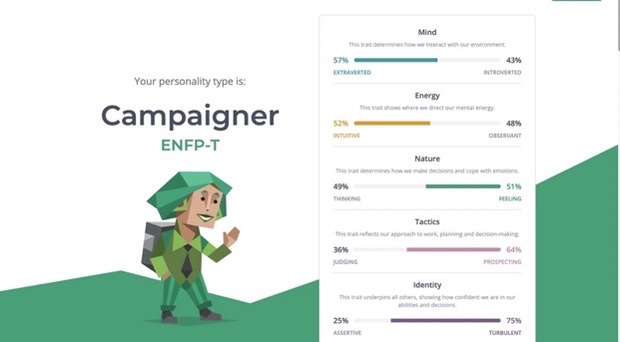
- The test was interactive because the site responded to the user’s input which also influence the person’s perception in considering the result of their answers.
- They reinforced complementary survey which after you answer it, they will analyze the results and publish it. They validate it by using advances of psychology to gather the accurate and fit variables and complexities of human personality.
- I think the site is trustworthy because it is properly cited and link to sources that are credible and relevant. And for the results, It is believable because I, myself witnessed the accuracy of the test and based on the ratings below all of them said that the test are accurate for them too.
ASSIGNMENTS
Assignment No.1
Define Computer
Computer is an electronic device for storing and processing data, typically in binary form, according to instructions given to it in a variable program. What defines a computer’s ability to understand natural language is its ability to parse the natural language and also execute the task intended.
Assignment No. 2
Connection of Internet and World Wide Web
The link between the World Wide Web and the Internet is that the Internet is a series of linked computers in gateways through which information stored in databases and on servers is transmitted from one computer to another, and that the World Wide Web is the program used to retrieve users’ requested information. The internet is a network of computer systems, stored data, some static things, some interactive things that can be accessed by using the word WWW before the address you want to go to.
Assignment No.3
RULES OF NETIQUETTE
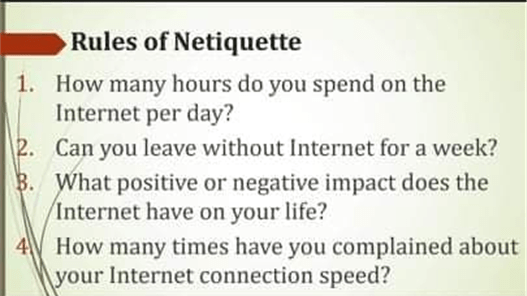
- 21 Hours per day
- If there’s a pandemic then I can’t.
- The provider positive effects are I don’t get bored, I can communicate with people, keeps me discover new things, Happy and enjoying, and gather some information. The negative effects are I don’t get enough sleep, I tend to see some bad things, learn bad things, and made me addicted.
- These past few days, our Wi-Fi connection is acting up so I always get disconnected during online class. We already complained to our network service but they still haven’t fixed so we thought of changing our service.
Acitivity No. 4
THINK Acronym
T- Threats can be anywhere
H- Harmful outcomes will occur if you’re not cautious
I-Invasion of privacy can happen on the internet
N-Never share your information recklessly
K- Knowledge is your treasure, use it to protect yourself
PERFORMANCE TASKS
Performance Task No. 1
Cybercrime Poster
